In the today’s digital age and use all over the world, maintaining the security of an organization has become more crucial than ever before – so watch out! 👀🔐
Sometimes, it is necessary to monitor organizational activities keenly to keep them away from serious exploitation. I am pretty sure that every organization might depend on at least one application to manage the entire Office 365 infrastructure
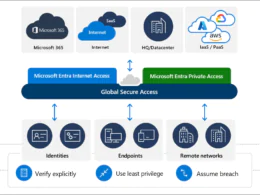
With a significant increase in the number of cyber threats, it has become essential to monitor and analyze sign-in data to minimize the risk of security breaches. That’s where Azure Active Directory and Usage & insights reports come in.
These comprehensive reports offer an application-centric view of the organization’s sign-in data, enabling admins to take proactive measures to enhance security and see vectors in your enviroment!
Among those reports, one of the most significant reports is the Azure AD application activity – currently in preview as this post is written. This report allows admins to generate sign-in activities for various applications in the organization. Now, let’s take a closer look at how this report can benefit organizations and help them enhance their overall security posture!
Who Can Access “Usage & Insights” Reports in Azure AD?
Find the license requirements to access the Azure Active Directory Usage and insights reports below.
- Azure AD tenant
- Azure AD premium (P1/P2) license
Next, make sure you have been assigned one of the following roles: Global Administrator, Security Administrator, Security Reader, or Reports Reader. Once you have these prerequisites in place, simply sign into the Azure portal and navigate to:
Azure Portal > Azure Active Directory > Usage & insights > Azure AD Application Activity (Preview)
Take a look!
Usage and Insights of Azure AD Application Activity Report
Application activity report in Azure AD provides valuable insights into the sign-in attempts of services and applications in the organization. It allows admins to find answers to questions like,
- What are the top used applications in my organization?
- Which applications have the most successful sign-ins?
- What applications have the most failed sign-ins?
- What is the top sign-in error for an application?
It is also important to note that the sign-in activity of a deleted application may still appear if it occurred during the selected date range. Additionally, if a user attempts to sign into an application without a service principal, this activity may also appear in the report. In these cases, it is necessary to review the sign-in logs for further investigation – take a look at it, it can suprice you! 🫢
What is the Need for Monitoring Activities in Microsoft 365?
As an admin/security guy, it is necessary to check user activities on a regular basis. Microsoft 365 auditing makes this simple.
However, most admins prefer PowerShell scripts for auditing over Audit logs due to its efficiency. As most attackers these days target sign-in activities to intrude into your organization, it is necessary to monitor user activities reports such as login history and last logon time to keep things on the right track. To ease these monitoring processes, admins/security may go for Azure AD applications. As same as the user activity is taken into account, Azure AD application activity is also another factor to consider.
What Details Can Be Obtained from an Application Activity Report in Azure AD?
Find the list of details that admins can obtain from an Azure AD application activity report below.
- Successful sign-ins count for each application.
- Failed sign-ins counts of each application.
- Success rate of each application.
- Sign-in activity graph for each application.
- Reports for the Application sign-in data for the last 7 days to 30 days.
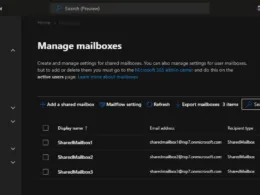
Sort the columns in descending order to find which application has the most successful sign-ins, failed sign-ins, and success rates. If you specifically want to look over an application, you can utilize the ‘Search’ box.
View Sign-in Activity in the Azure AD Application Activity Report
Sign-in activity graphs provide admins with a visual representation of the spike and fall in sign-in attempts over the last 30 days, 7 days, or 1 day. This information can be used to understand the usage patterns and trends of applications in the organization.

In the above graph, the blue and pink lines represent successful sign-ins and failed sign-ins, respectively. Further, admins can also find the reason for sign-in failure down to the sign-in activity graph that includes details such as error, error code, sign-in failure occurrence count, and last seen.
Remember when I mentioned that the sign-in attempts to an application could show up in the activity report even if there was no service principal involved? You may wonder what a service principal really means!
Some key features of Azure AD Application Activity Report Analysis
- User Sign-In Activities: Gain visibility into user sign-in activities across your Azure AD environment. Monitor successful and failed sign-in attempts, track sign-in locations, and identify any suspicious activities.
- Application Usage Insights: Understand how your applications are being utilized by users. Analyze usage patterns, identify popular applications, and determine the frequency and duration of application sessions.
- Security Event Monitoring: Detect and investigate security events and anomalies within your Azure AD environment. Identify potential threats, such as multiple failed sign-in attempts or unusual access patterns, and take appropriate actions to mitigate risks.
- Risky Sign-In Detection: Azure AD Application Activity Report Analysis includes built-in algorithms that identify risky sign-in events, such as sign-ins from unfamiliar locations or unusual devices. Get alerts and notifications for such events and implement additional security measures if needed.
- Anomaly Detection: Leverage machine learning capabilities to identify abnormal user behavior and access patterns. Detect potential insider threats, compromised accounts, or unauthorized access attempts.
- Compliance Reporting: Generate comprehensive reports for compliance auditing and regulatory requirements. Capture and retain relevant activity logs and security events to demonstrate adherence to data protection standards.
- Customizable Insights: Tailor the analysis based on your organization’s specific needs. Apply filters, create custom queries, and focus on specific applications or user groups to obtain granular insights.
- Real-Time Monitoring: Monitor user activities and security events in real-time, enabling you to respond promptly to any potential threats or breaches. Stay informed about critical activities happening within your Azure AD environment.
- Integration with Security Solutions: Azure AD Application Activity Report Analysis can be integrated with other security solutions, such as Azure Sentinel or Microsoft 365 Defender, for enhanced threat detection and incident response capabilities.
- Historical Data Analysis: Access historical data to perform trend analysis, identify patterns over time, and gain deeper insights into application usage and security trends within your Azure AD environment.
What is a Service Principal?
A service principal is a special type of account that represents an application or service rather than a user. When a service principal needs to access resources, it uses its own credential, such as a certificate or app secret, to authenticate and gain access. Think of it as a secret key that only the application knows and uses to unlock the resources it needs – and nothing more!
What is a Service Principal Sign-in?
Service principal sign-ins are unique in the way that they don’t involve a user at all. Instead, they’re sign-ins by non-user accounts like apps or service principals, which use their own credentials to authenticate and access resources.
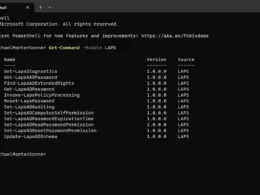
To monitor service principal sign-ins, Microsoft introduced a new preview report under Azure AD Usage & insights named Service principal sign-in activity to make work easier. In this report, you can find details of the application name, last sign-in date, application ID, and other details.
By clicking on View more details, you can gain information on the application’s client ID and object ID.
In case of any issues with the application’s authentication, the client ID and object ID can be used to trace the issue by reviewing logs and audit trails in Azure AD. This information can help you identify the root cause of the issue and take corrective actions.
Conclusion
In today’s workplace, Microsoft 365 third-party applications have become essential tools for employees to perform their job responsibilities. Consequently, it has become crucial for administrators to keep track of application activity within their organization.
See more here: Usage and insights report – Microsoft Entra | Microsoft Learn
Note: Please keep in mind that the availability of specific features may depend on your Azure AD subscription and the configuration of your environment – some features is still in preview (as this post is created)
Thank you for taking the time to visit my blog. Kindly share it with others if you find it helpful for them! 😉🔐👍
Stay tuned for the new post about something cool! 🥳