Last Updated on February 21, 2024 by Michael Morten Sonne
Intoduction
In Public Preview as this post is written
This is part 1 and is about what Global Secure Access is – see the next parts for setup, installation and configuration!
In an dynamic nature of work, where teams operate across diverse locations, the need for secure and efficient connectivity has become paramount. Microsoft’s Global Secure Access emerges as a game-changer, revolutionizing the landscape of secure connectivity. In this introduction, we’ll explore what sets Global Secure Access apart from traditional VPNs and how it seamlessly integrates with Microsoft Entra ID to elevate the standards of network security and controll access to resources.

Before delving into the parts of Microsoft’s Global Secure Access, let’s acquaint ourselves with fundamental concepts about what is a part of this solution:
ZTNA – Zero-trust Network Access
ZTNA represents a security model that explicitly verifies and continuously validates access requests based on received signals. It operates on the principle of zero trust, requiring robust authentication and stringent device compliance.
SSE – Security Service Edge
SSE encompasses all the aforementioned services, excluding SD-WAN, providing a comprehensive security framework for organizations.
SASE – Secure Access Service Edge
SASE is an all-encompassing approach to network security, merging network connectivity and security functions into a unified cloud-based service. It ensures secure access to cloud applications, data centers, and the internet from any location.
CASB – Cloud Access Security Broker
CASB solutions empower organizations to monitor and control interactions between users and cloud applications, enforcing security measures such as blocking file downloads and preventing data loss.
SWG – Secure Web Gateway
SWG solutions shield organizations from internet threats by blocking access to specific URLs, filtering content, and thwarting access to particular website characteristics.
FWaaS – Firewall as a Service
FWaaS utilizes cloud-based firewalls to safeguard networks and applications without relying on on-premises hardware.
SD-WAN – Software Defined Wide Area Network
SD-WAN is a technology enabling users to connect to a cloud provider’s global network, eliminating the need for traditional MPLS connections.
I think that is the overview of the parts in short therms! 😉
Prerequisites
The preview requires a Microsoft Entra ID P1 license. If needed, you can purchase licenses or get trial licenses. To use the Microsoft 365 traffic forwarding profile, a *Microsoft 365 E3 license is recommended. After general availability, Microsoft Entra Private Access and Microsoft Entra Internet Access might require different licenses.
*I’m unclear about the the information behind this suggestion, but we can speculate that it might be a feature exclusive to Microsoft 365 Apps for enterprise or so in the future?
I hope it remains inclusive of the Business Premium license to for many SMBér! 🤞
Administrators who interact with Global Secure Access preview features must have the Global Secure Access Administrator role. Some features might also require other roles in the future.
To follow the Zero Trust principle of least privilege, consider using Privileged Identity Management (PIM) to activate just-in-time privileged role assignments.
Key highlights
- Security through Identity-driven Access based on Entra ID: Enhance security measures by prioritizing identity-driven access control – and is based on the principles of Zero Trust.
- Integrating with Conditional Access policies to enforce access controls and a lot of other requirements!
- Cloud-Native Networking Objectives: Transitioning to a cloud-native approach in networking with the primary goal of better security by:
- Seamless Boundary Crossing: Facilitating smooth transitions across the corporate/private network and the public network in general
- Optimal Connectivity with Microsoft’s Global Network Backbone: Is’s utilizing the big global network backbone at Microsoft to optimize connectivity for enhanced performance based on your location
- Can Applying policy profiles and efficiently routing traffic.
- Establishing web filtering policies based on your needs! 🔐
Security Focus
The security part is paramount within this context. From my perspective, it revolves around the following key points:
- Entra ID: The entire suite of new products hinges on Entra ID, encompassing ID protection and Conditional Access. This framework ensures secure authentication, application of tenant restrictions, and the detection and correlation of (risk) signals and activity data – all guided by the principles of Zero Trust.
- Global Secure Access Client for Windows: The Global Secure Access client, designed for Windows and more OS’es over the time as the solution is developed, operates as a small agent with capable of monitoring and directing network traffic across the Microsoft backbone. It offers the ability to implement controls seamlessly.
- Defender for Cloud Apps Integration: Defender for Cloud Apps plays a pivotal role by providing deeper insights into the realm of cloud security access brokerage (CASB) as many forget. Positioned between the communication of your identities and cloud applications, it empowers the establishment of policies governing app governance.
- Flexible Network Configuration: Alternatively, you can configure a remote network where your customer premises equipment (CPE) connects to the Global Secure Access service via an IPSec tunnel. This method eliminates the need for client installations but is contingent upon the network’s configuration. (I have not the needed equiments for testing this part)
Global Secure Access vs a normal VPN
Traditional Virtual Private Networks (VPNs) have long been the go-to solution for securing remote access to corporate resources. However, as the way we work continues to evolve, Global Secure Access steps in to address the limitations of conventional VPNs. Unlike traditional VPNs, which often come with complexities and performance bottlenecks as all client is useing the same specific way in and out of the network/firewall, Microsoft’s Global Secure Access embraces a Zero Trust model, offering a more robust and flexible approach to network security and identity based access when the access it happening (user will connect).
The traditional VPN model typically provides a blanket security layer, granting access to the entire network or subnets once a user is authenticated. This presents a security threat, as individuals with compromised credentials may obtain access to various resources, potentially resulting in reconnaissance and lateral movement.
In recent efforts to enhance the security of many companies using etc. Entra ID for central management of identityes, many have been diligently working on transitioning to passwordless authentication, implementing phishing-resistant credentials, and ensuring compliance with devices through Conditional Access.
Many have functional VPN´s (like myself at home – but looking at this private for my uses), but the current VPN solutions encounters challenges in etc. supporting Entra ID authentication for end-users in many solutions.
In contrast, Global Secure Access employs a Zero Trust approach, ensuring that users and devices must continually prove their identity and adhere to the principle of least privilege. This paradigm shift enhances security by reducing the risk of unauthorized access and potential data breaches.
Confronted with the realization that the existing legacy VPN´s may never embrace native Entra ID authentication, so lets now explore Microsoft Entra Private Access/Global Secure Access! 🥳
Integration with Entra ID
One of the key distinctions of Global Secure Access is its seamless integration with Microsoft Entra ID. Entra ID serves as the backbone of identity management within the Global Secure Access framework and all your Azure and Microsoft 365 services, ensuring that only authenticated and authorized users gain access to corporate resources here when needed. This integration extends the capabilities of Entra ID, providing a unified portal within the Microsoft Entra admin center.
Through this integration, Global Secure Access simplifies access policy management. It enables real-time monitoring and adjustment of user access based on changes in permissions or risk levels, offering a level of adaptability that traditional VPNs struggle to match. This unified approach ensures a cohesive and comprehensive security strategy, aligning identity management with network security for a more holistic defense against evolving cyber threats.
In the following exploration of Microsoft’s Global Secure Access, we will delve deeper into its features, benefits, and the transformative impact it brings to secure connectivity. Join me as we navigate through the future of network security, leaving behind the limitations of traditional VPNs in favor of a more agile and sophisticated solution.
Types of profiles
Distinct treatment can be applied to the traffic from three app/resource channels for now:
- Microsoft 365 – encompassing all traffic directed to Microsoft network endpoints.
- Private Access – covering traffic to on-premises hosted apps (yes, like the old App proxys!)
- Internet Access – including traffic to any other network or the internet.

The approach – Global Secure Access
To overcome the limitations of traditional VPNs, Microsoft’s Global Secure Access solution aims to deliver heightened security and improved accessibility. Here are the distinguishing features that set it apart:
The benefits of Security Service Edge (SSE)
Microsoft’s SSE successfully addresses the following challenges as it is now:
- Cloud scalability, performance, and redundancy are integrated in the hole solution🦺
- Clients connect to the nearest Point of Presence (POP), ensuring optimal performance – and from here you are using the backbone in Microsoft´s Infrastucture 🚀
- Access is granted to cloud apps, websites, on-premises apps and multi-cloud environments.
- Security controls, such as DLP, SWG, and FWaaS are available if required for your needs.
SSE effectively tackles security concerns by aligning security measures with modern digital environments. In these dynamic landscapes, where workloads, devices, and users are in constant motion, traditional perimeter-based security models prove ineffective.
Requirements for SSE Cloud Providers
For SSE solutions to operate effectively, they need:
- A swift, dependable and secure global network (Microsoft have this!)
- Identity and access management grounded in a zero-trust framework – you have that too right? 😉
- Virtualized services that are high-performing, reliable, and scalable.
- Geographically distributed Points of Presence (POPs) to ensure efficient access.
Microsoft fulfills all these criteria, establishing itself as a reliable option for organizations in search of secure global access.
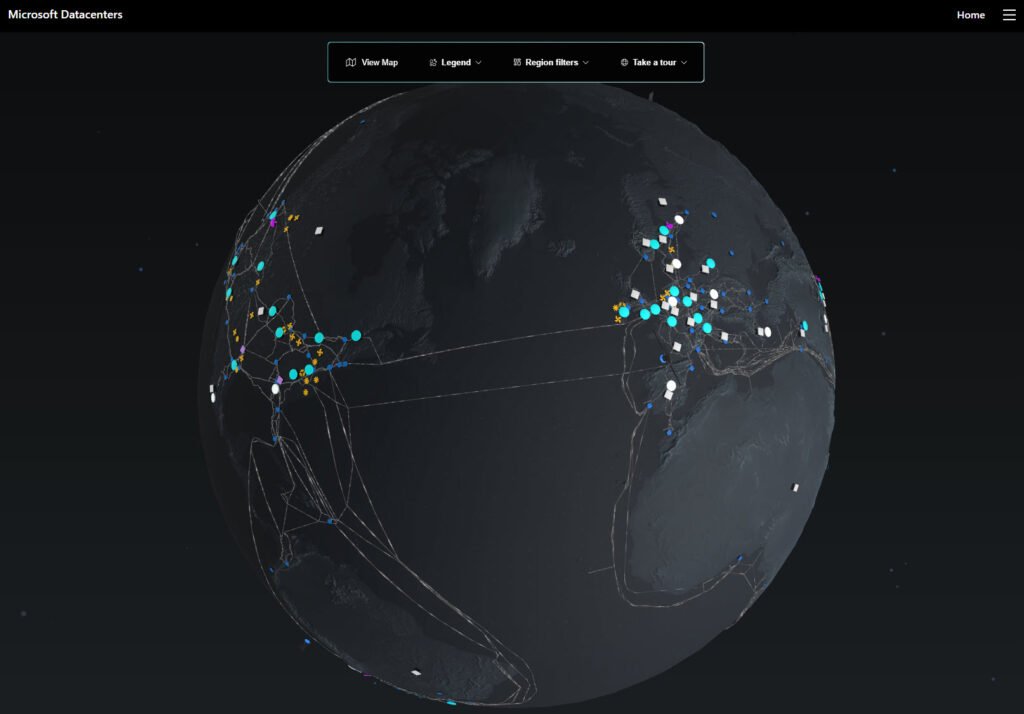
Discover a world of infrastructure with Azure in this nice Globe view where you can explore the Global Infrastucture: Azure global infrastructure experience (microsoft.com) – it´s very nice to Explorer this Globe (and Denmark is comming to with 3 Datacenters soon!! 🤩🌍)
How does it work
(This is some interesting stuff – that is here it is special)
Solution for end-users and devices
Connectivity from Client to App
Within Microsoft’s SSE solution, clients undergo authentication through Entra ID & Condentional Access profiles to establish a secure and authenticated tunnel to the service. The routing of traffic through the global secure network is determined by traffic forwarding profiles, with additional security controls applied as needed. This ensures secure access to Microsoft 365, cloud SaaS apps, internet websites, on-premises apps, and multi-cloud environments if needed by you.
Enhancing Layers
Here we add more layers of “onions” to the connection 🔒
Devices must be either joined to Microsoft Entra ID (recommended way) or hybrid joined; registered devices are not compatible. By introducing this additional layer of protection in the prerequisites, it significantly heightens the difficulty for attackers to exploit the solution. This stands in contrast to traditional VPNs, where stolen configurations and credentials can be utilized on virtually any device.
Solution for Branch Offices
(I have not the stuff needed to test this, so I will not cover blogs about this)
In the context of branch offices, the implementation of remote network links via IPsec/IKEv2 from Customer Premises Equipment to the edge offers identical features. Border Gateway Protocol (BGP) is employed for efficient route advertisement. Hare we go into network stuff I know a bit of, but im not an expert here 😅
Challenges in Modernizing Remote Networks
Bandwidth requirements have grown – The number of devices requiring Internet access has increased exponentially. Traditional networks are difficult to scale.
Remote networks commonly utilize connectivity methods like site-to-site virtual private networks (S2S VPN) or rely on a dedicated Wide Area Network or Multi-Protocol Label Switching (MPLS). The issue with these conventional technologies lies in their scalability challenges. Moreover, with the increasing adoption of Software as a Service (SaaS) applications like Microsoft 365, the demand for low-latency and jitter-free communications continues to escalate, posing a significant hurdle for traditional approaches.
Why you might get value from remote network connectivity
Ensuring the security of a corporate network has become more challenging in the era of remote work and dispersed teams. Security Service Edge (SSE) introduces a paradigm where users can securely access corporate resources from any location globally, eliminating the necessity to funnel their traffic back to headquarters.
To learn more about secure remote network-to-remote network connectivity, see the Azure Virtual WAN documentation.
How It works
The connection of remote networks to Global Secure Access involves configuring an IPSec tunnel between your on-premises equipment and the Global Secure Access endpoint. This configuration directs specified traffic through the tunnel to the nearest endpoint, allowing the application of security policies from the Entra admin portal.
Why remote networks
Utilizing remote networks as an alternative method for deploying Global Secure Access. eliminates the need to install the GSA client on each devices in that network. This is particularly beneficial when dealing with static devices in a hole office or when users and devices are physically located in a specific area. Additionally, considering that the GSA client is currently supported only for Windows 10/11, remote networks provide a solution for devices such as Linux systems, IoT devices, video cameras, printers, etc. These devices’ traffic can be monitored and secured via the Global Secure Access tunnel and endpoint, offering a comprehensive and flexible solution for your devices on the network.
Microsoft Entra admin center
Discover the power of Global Secure Access, your centralized hub within the Microsoft Entra admin center for configuring and managing Microsoft Entra Internet Access and Microsoft Entra Private Access.
Go to https://entra.microsoft.com and exploring the features and capabilities that Global Secure Access has to offer. Elevate your network management experience with Microsoft Entra – your key to a secure and efficient digital workspace.

The installed client
Whether from the desktop client or a remote network like a branch location, the installed client effortlessly acquires network traffic, providing a dedicated public internet traffic forwarding profile. Experience fast, secure, and compliant access to public internet apps while leveraging Microsoft’s identity-aware Secure Web Gateway solution.

Explore the various tray icon options available (for now) when logged in with your Entra ID credentials:

Stay tuned for more insights in Part 2, where we guide you through the activation process and client installation. Don’t miss the chance to elevate your network security game!
Conclusion
In part one of our exploration into Microsoft’s Global Secure Access, we’ve witnessed a paradigm shift in network security, driven by the evolving nature of the modern workforce. With Security Service Edge (SSE) at its core, Global Secure Access unifies Microsoft Entra Internet Access and Microsoft Entra Private Access, offering a dynamic and secure solution rooted in Zero Trust principles.
This comprehensive security framework streamlines access policy management, orchestrates secure access, and ensures continuous monitoring for real-time adjustments. The global network spans 140+ countries and 190+ network edge locations, providing optimal connectivity for users and devices to public and private resources.
As we conclude part one, it’s clear that Global Secure Access is reshaping the future of network security.
Stay tuned for Part 2, where I will guide you through the activation of features and the seamless installation of clients in Global Secure Access. Uncover the step-by-step process to harness the full power of this innovative solution, ensuring a smooth and secure activation of features and effortless deployment of clients across your network. Don’t miss out on the practical insights that will empower you to make the most of Global Secure Access in your organization. Watch out for the upcoming details!
Thank you for taking the time to visit my blog. Kindly share it with others if you find it helpful for them! 😉🔐👍
Stay tuned for the new post about something cool! 🥳
References
Global Secure Access documentation – Global Secure Access | Microsoft Learn